AARP Hearing Center
There has been a proliferation in the availability and use of data. The need to protect this information against unauthorized access has become increasingly important. Policymakers and the private sector play important roles in establishing the guardrails that allow data uses that bring lasting consumer benefits and are aligned with AARP’s Consumer Data Privacy and Security Principles.
Some types of data are sensitive and need heightened protections. For example, unauthorized disclosure of health, financial, and precise location personal information is especially harmful. Social Security Numbers (SSNs) likewise need heightened security protections. They are used for a wide range of purposes unrelated to Social Security and thus are particularly valuable to identity thieves. They can be used to assume the identity of another individual and commit fraud. Agencies and businesses are routinely replacing SSNs with specialized ID numbers to better protect customers’ identities. For example, in 2018, new Medicare cards began using a Medicare-specific number on them in place of an SSN.
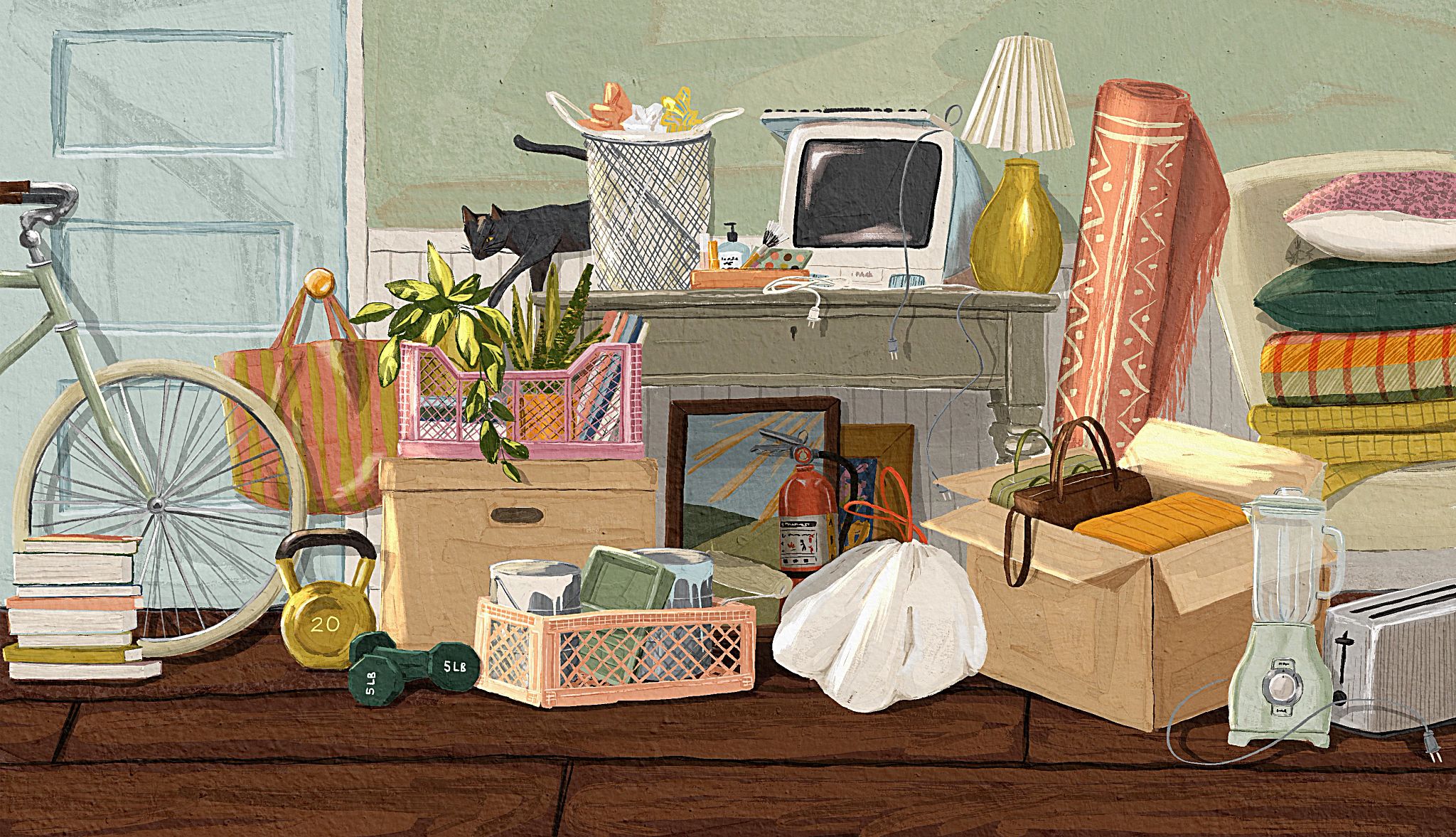
In addition to these concerns, internet-connected devices are increasingly becoming part of everyday life. These devices are able to communicate and interact with other devices and external networks to share data. They include smartphones, smart watches, appliances, fitness trackers, thermostats, and cars. The rapid spread and growth of connected devices have outpaced the development of security safeguards necessary to protect consumers. Studies have found security vulnerabilities common in all types of connected devices.
One concern is that hackers will compromise connected devices to gain access to consumers’ sensitive personal information. Another is that hackers can exploit security weaknesses to gain control of the device itself. Once in control, the hackers can cause the device to function incorrectly or use it in unexpected ways. In addition, hackers are using compromised devices to carry out large-scale cyberattacks aimed at disrupting large websites.
Experts recommend that product developers build strong security protections into connected devices from the earliest stages of product development. Devices should be “secure by design.” This means that the device has been designed from the ground up to ensure security. Security protections are in place immediately. Consumers do not have to take additional steps to configure the device for greater security.